In the not-so-distant future, our digital landscape may face a profound transformation. This precipitating moment, often referred to as Q-Day, signals the dawn of a new age in cybersecurity, where quantum computing unlocks the vault of humanity’s most intimate secrets. Imagine a world where our private communications, financial transactions, and even sensitive medical records become accessible to anyone wielding a sufficiently advanced quantum computer. The consequences are staggering, and the discussion surrounding this impending reality is ripe with urgency.
Cybersecurity experts have likened this impending shift to playing Russian roulette. Michele Mosca, a prominent voice in the field, articulates the fear that accompanies these advancements: with estimates suggesting a one-in-three chance that Q-Day may arrive before 2035, there’s palpable tension. The idea that this day may already be upon us—albeit shrouded in secrecy—adds another layer of complexity. The potential for a secretive breakthrough in quantum computing only heightens the stakes.
The Quantum Race: Who Will Lead the Charge?
As debates about the ramifications of Q-Day intensify, an undercurrent of competition fuels advancements in quantum technology. Global tech giants like Google, IBM, and Microsoft’s relentless pursuit of quantum innovation is not just a quest for technological supremacy but also a race to seize control over cryptographic infrastructures. Meanwhile, nations like China are pouring significant resources into their quantum advancements, motivated by the dual promise of transformative technology and unparalleled security risks.
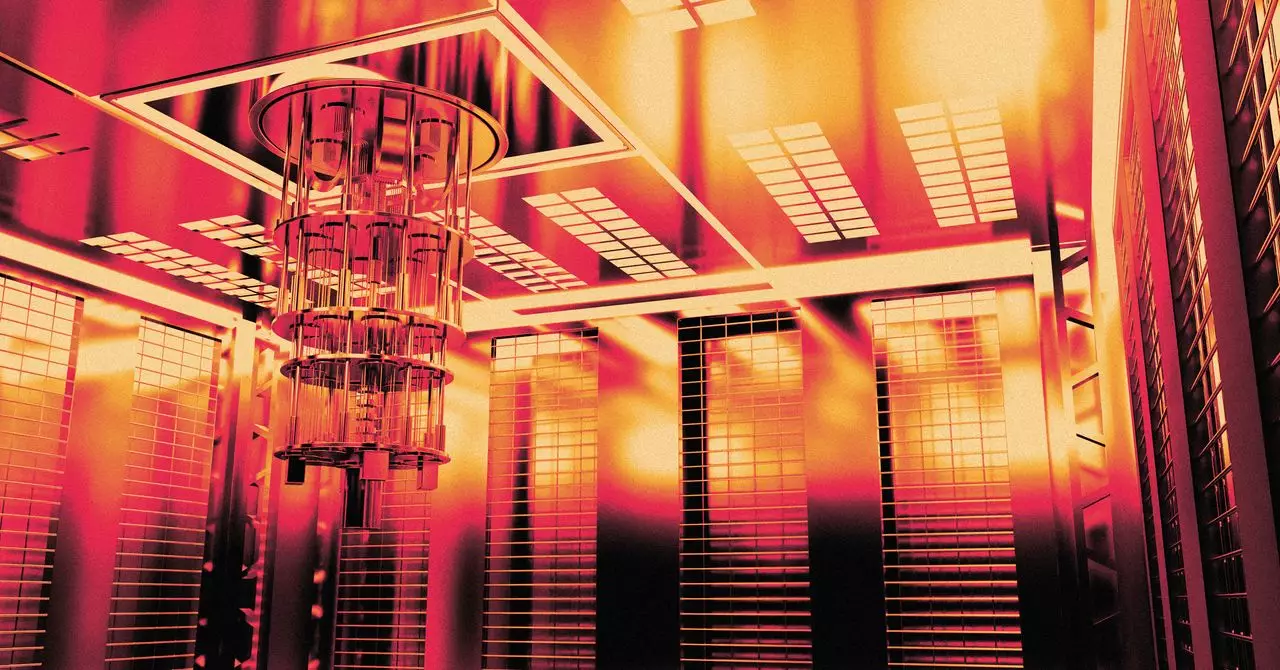
The implications are profound. In a landscape where quantum computers could unravel encryption methods that have safeguarded our data for decades, the line between innovation and security has never been more blurred. Quantum technology operates on principles markedly different from classical computing, harnessing the properties of quantum bits, or qubits. This not only offers enhanced computational power but also poses unprecedented challenges in data protection. For instance, while classical computers operate linearly—calculating one option after another—quantum systems can assess multiple possibilities simultaneously, dramatically amplifying their capability to crack codes.
The Potential Scenarios of Q-Day
What would Q-Day look like? The answer is as complex as the technology itself. It might unfold in various ways, from a discreet unveiling of vulnerabilities to a catastrophic breakdown of critical systems. One chilling possibility is the gradual revelation of security breaches, emerging as disjointed news reports—a power grid blackout in London during an election, perhaps, or sensitive government data leaking online. The chaos could cascade, leading to widespread distrust of our digital systems, as disparate incidents gradually coalesce into a realization: the age of cybersecurity is over.
Alternatively, the handle of this universal picklock might prefer the dramatic—an all-out assault on civilization’s digital backbone. Quantum malicious actors could theoretically disrupt energy grids, disable military systems, or unravel financial markets simultaneously, creating havoc on an unprecedented scale. The byproduct? A chaotic scramble as we attempt to comprehend the magnitude of these breaches and their consequences.
Preparing for the Quantum Future
While the specter of Q-Day looms large, there is much we can do to fortify our defenses against the potential fallout. Recognizing that traditional encryption methods may fall prey to quantum powers, researchers are advocating for the development and adoption of quantum-resistant algorithms that can withstand these emerging threats. Governments and organizations must invest in advancements that prioritize cybersecurity in the quantum era, fostering collaboration across sectors to ensure a unified front.
Moreover, heightened public awareness is crucial as we navigate this new frontier. Educating society about the risks and realities of quantum computing empowers individuals to take proactive measures in securing their data. From advocating for better security practices to demanding transparency from service providers, individuals have a vital role in the collective defense against the quantum threat.
As we stand on the precipice of this quantum revolution, it is imperative to grasp the implications of Q-Day not just as an existential threat but also as a challenge beckoning for innovation, collaboration, and resilience. Let us confront the uncertainty ahead with clear eyes, proactive strategies, and a commitment to safeguarding the world’s secrets amidst the unfolding quantum dawn.

Leave a Reply
You must be logged in to post a comment.